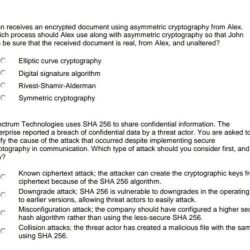
John Receives An Encrypted Document Using Asymmetric Cryptography From Alex
In the realm of digital security, John receives an encrypted document using asymmetric cryptography from Alex, a captivating tale that unfolds the intricacies of this enigmatic field. Asymmetric cryptography, a…
Read more »